Bringing the Blue Screen of Death to Court
A former exploit writer and penetration tester's musings on criminal cases
I compoop.
That’s not a typo. It’s a reality, friend.
A rough translation is that I have used, abused, and written about computers in some form or another for over twenty years. Most of my writing is related to Python, the programming language I used to teach hacking and exploit writing. Not how to hack into things, rather, how to build the tools to hack into things. How to “live off the land” as it’s known in the hacking world — the ability to hack into a system and stay there, using what’s available on the system and network to remain undetected and present as long as possible.
I compoop.
I know compoopers pretty good. Beep boop!
So, I’ve always found it funny how, when I’m working on criminal cases, people seem surprised that I’m able to spot small discrepancies hidden among thousands of pages of discovery.
It’s easy.
Everything I learned, I learned from hackers
I don’t recall the exact journey from diaper-adorned, hobbyist VCR disassembler in the 1980s to working for one of the best teams of hackers in the world in 2008. But it’s true.
Immunity was a small, wily team of hackers who, at the time. numbered about a dozen and hailed from Argentina, Turkey, New Zealand, Italy, USA, the Netherlands, France, and I was the lone Canadian1. Quite honestly, I don’t know where a couple of them were actually located. Our headquarters was a large converted house in Miami Beach, Florida. You could get shit on by a parrot in the backyard during a cigarette break.
We were led by a genius duo of former government hackers, Justine Bone and Dave Aitel, from New Zealand and the USA, respectively. Although names have changed and everyone has since moved on, in the early 2000s and beyond, Immunity was publishing some of the most cutting-edge hacking research you could find.
I, on the other hand, was like the dude who’d show up, accidentally light the garbage can on fire, spill coffee into your CD-ROM drive trying to put that fire out, and then piss his sweatpants from anxiety as a result2. To say I was in awe of my colleagues is an understatement, and I truly felt like I had to work my ass off just to be there every day.
When I joined the team in 2008, one of my first assignments was to reverse engineer a Microsoft Windows “driver”, and develop an exploit for it.
The problem is that I didn’t know jack shit about reverse-engineering Windows drivers in 2008.
Reverse Engineering Security Patches & Criminal Discovery
When you plug a new mouse into your laptop, and it chimes, then connects, behind the scenes, your computer has detected that you plugged in a mouse, figured out the type of mouse it is, and then loaded a special piece of software called a driver. Drivers act like a bridge between the physical world, like you moving a mouse, and the operating system you interact with, like Microsoft Windows. A driver works to translate your physical movement into a cursor moving across the screen. There are countless types of these little suckers on your system right now, managing everything from printing documents to the packets being sent over your WiFi to read this article.
Drivers are also software, like a web browser or a file server, that can take input from a user (or a hacker) and take action on it. It is here where the danger lies; whenever software has to take some form of input is where things can go awry and where the ‘holes’ exist that hackers exploit to take control of a system. Once these holes are identified, much like a bullet hole in the stern of a ship, software vendors scurry to close them up, or ‘patch’ them. Hence, the term patching.
When my aged ass was still writing exploits, anytime Microsoft released a new security update for Windows, hackers from all over the world would begin examining the changes in their systems before and after the patch was applied.
This is called diffing, where you compare line-by-line changes in code or configuration files on a computer to see what has changed — or is different — between them. This process would then allow a hacker to home in on the security problem that had just been fixed by Microsoft and the code responsible. This now gives the hacker a toehold to start figuring out how to exploit the security vulnerability (before the update was released), so that they can then break into any system that doesn’t apply the updates.
Diffing and auditing code is tedious, tiring, mind numbing work. The more you are wired to stay at it, the better you are at finding holes. This is no different from being presented with thousands of pages of discovery and terabytes of evidence. There’s no AI that’s going to replicate the methodical and careful reading and absorption of code or criminal discovery.
This diffing process by hackers is also why automatic updates and a fully patched system, to this day, remain among the best guards against exploitation. Hackers look backwards in time, reverse-engineer the patches, and then try to catch you with your proverbial patch pants down.
This process is similar to approaching a criminal case that has already been tried. You have the opportunity to examine where there were vulnerabilities probed, areas of weakness identified the first time around, and where the prosecution may have attempted to ‘patch’ something that hides a previous vulnerability; you can now return to exploit. Suppression hearings, Daubert transcripts, and expert reports are where I usually start this process.
The inverse is when we were attempting to find vulnerabilities in a system that had no patch to reverse-engineer in the first place. This is the first trial, and I am relying on applying a systematic review process to identify the most common vulnerabilities. Vulnerabilities are case-specific, just like they are software-specific, but having a systematic way to identify the lowest hanging fruit first is always crucial. Build checklists, templates, or whatever works for you, but it should be systematic so that you notice when something is a ‘gotcha’ or deviates from a ‘normal’ case’s baseline.
So, anyway, I began reverse engineering and testing this driver from Microsoft.
I learned a few things along the way.
I Smell Burnt Toast
You only get one shot, do not miss your chance to blow
This opportunity comes once in a lifetime, yo
Eminem
In Canada, we had Heritage Minutes, short commercials that ran on television, compressing important moments in Canadian history into 60 seconds. One of the more famous ones is the story of Dr. Wilder Penfield, who developed surgical procedures to treat epilepsy. The commercial shows the patient’s brain being probed, and various reactions as a result, with the ultimate exclamation that she can smell burnt toast — a sign of an oncoming seizure.
This is very much akin to writing Windows driver exploits.
You have to imagine, as a hacker, you have already gained access to a system because someone made the mistake of opening a booby-trapped email attachment. Now you have some control over the victim’s system, but you are not guaranteed to be the system administrator account. It is the administrator account that allows you to steal additional secrets, such as passwords, silently install more software, or make changes to the victim’s system; something a regular user may be prevented from doing.
This is where being able to exploit a Windows driver becomes incredibly useful. Drivers are operating deep in the brain of Windows. If we can trick that driver to do our bidding, then it’s bidding will be in the brain. The right probe to the driver, and we use it to carefully nudge little bits of computer memory around, flipping your account from a regular user to a system administrator.
It’s a small, subtle change that you are making at the very core of the brain that is powering that computer in that moment. Do it right, and the process is all blind to the victim at the computer.
Screw it up? Sneeze with the probes in your hands and the patient’s skull open?
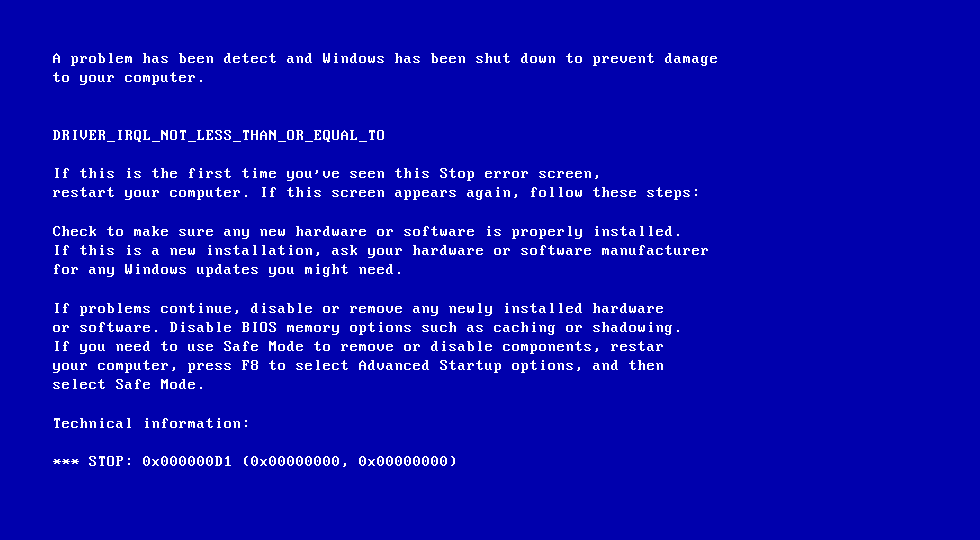
Your victim, sitting at their computer, will get a blue screen of death, and your connection and access to their system will be lost.
That’s a bad day.
It’s worse if that happens on a central server powering a number of services, because now you’ve knocked out a whole bunch of shit, and you better believe the incident responders are coming.
This is what happens when a lack of due diligence on a witness, an expert, or simply failing to thoroughly investigate a case will just destroy you in a moment during a hearing. I have seen cases where the confidence of an expert wilts before the Court when it is found that they incorrectly disclosed their training or parts of their testimonial experience. You have one shot — make sure you have thought through all the possibilities you can, you’ve played devil’s advocate until you’re ready to throw up, and you’ve assessed risk repeatedly.
Witnesses or Windows, we want it smelling burnt toast, not dying on the table.
Some Tips from The Trade
The core methods I used as a penetration tester and exploit writer, I still use today, and there’s no special sauce or software involved, I assure you:
Take copious amounts of contemporaneous notes, and keep them organized — this used to be spiral bound notebooks as a penetration tester, and now is Remarkable.
Build timelines. This was a hard requirement for our reporting purposes at Immunity for exploit writing and penetration testing. For the love of all things holy, build a timeline of whatever it is you’re working on right now.
Assess risk, manage risk, reassess risk and test as much as possible before your one-shot exploit is fired. You pull the trigger on an exploit and the system dies, that’s on you — same goes in front of the jury.
Last but not least, when the time is right, show your work to the world.
Where confidentiality didn’t bar it, Immunity relentlessly educated. We weren’t alone, it was part of the culture in the industry.
I follow the same ethos in criminal cases.
If a report is being filed, it should stand on its own, have enough source material to reproduce the methodology by a third party, and be open to public scrutiny. It should also be an opportunity to teach — to help educate the Court, its participants, and any other attorney or expert that might read it in the future.
Community and knowledge transfer are crucial. And if you can handle being berated by hackers, you can handle being cross-examined.
Cliff and Minion, you came later, but you deserve not only a Canada nod but a Saskatchewan nod to boot. Bas, you’re always Canadian in my books.
At one point, I managed to check out the entire source code repository, somehow take ownership of every file, modified them all and checked them back in. No idea how but I do believe Bas was going to send me to Jesus if I touched the repository again.